 Winklix
WinklixIT Solution Simplified

World Trade Center, Sheikh Rashid Tower Level 24 Sheikh Zayed Rd Trade Centre 2 - Dubai - UAE
Delhi NCR | Mumbai | Pune : HQ : C -430 , Noida Sector 127 , Uttar Pradesh , 201313 , India
Business Units
Traditional security cannot keep up with today's automated threats. We embed AI-powered protection into your cloud using advanced behavioral analytics and machine learning to detect risks before they escalate.
Cut through alert noise with intelligent threat correlation, uncover hidden vulnerabilities, and respond instantly with automated remediation workflows. By implementing Compliance-as-Code, we ensure your infrastructure is continuously monitored, secured, and aligned with evolving industry standards.
Future-proof your cloud with resilient, intelligent, and secure architecture powered by Winklix.

We leverage CSPM tools to continuously monitor your cloud environment for misconfigurations and drift in real time, ensuring proactive and continuous security hardening.
Our analytics-driven approach prioritizes vulnerabilities based on real risk and exploitability. By implementing Compliance-as-Code, we automate policy enforcement and prevent non-compliant infrastructure from being deployed.
We enable intelligent access control based on user context such as location, device health, and behavior patterns to keep access seamless and secure.
Using machine learning, we correlate thousands of alerts into meaningful insights. Automated SOAR playbooks respond instantly to routine threats while your team focuses on critical incidents.
We implement zero trust principles where every user, device, and request is continuously verified, protecting your infrastructure against lateral movement and insider threats.
We embed security into your development lifecycle by integrating SAST and DAST into CI/CD pipelines so vulnerabilities are fixed before deployment.
AI-driven models anticipate attack vectors before they are executed, helping you stop breaches at the earliest stage and shift security from reactive fixes to proactive defense.
We build data-driven security strategies aligned with your business goals. With a virtual 24/7 vCISO approach, we ensure continuous compliance, risk monitoring, and decision-making that supports outcomes.
Our identity and access governance frameworks evolve as your business scales globally, helping you stay compliant with international standards while maintaining automated security across regions.
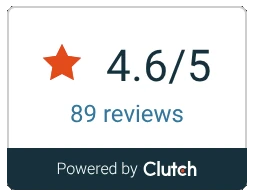
We align our success with our clients success : Our client-centric approach delivers clients satisfaction consistently .












We are proud to work with some of the most renowned brands in the world.

















We use advanced analytics and penetration testing to uncover weaknesses early before attackers can exploit them.
We implement layered security controls using cutting-edge technologies to protect your systems from evolving threats.
Our AI-driven systems detect, adapt, and respond to threats in real time, ensuring faster and more effective protection.
We streamline your security operations with continuous monitoring and automation for consistent, efficient performance.
We align your systems with global standards like GDPR and HIPAA, providing audit-ready security with complete compliance visibility.
 alt="Microsoft Consulting Services Visual"
alt="Microsoft Consulting Services Visual"
Grow personally and professionally at Winklix. Work with global teams, innovative technologies, and meaningful projects that help businesses transform digitally while unlocking your full potential.
Cloud governance frameworks define policies, controls, and best practices to manage cloud environments effectively. They help enterprises ensure security, control costs, maintain compliance, and align cloud operations with business and regulatory requirements.
AI-driven security uses machine learning and behavioral analytics to detect anomalies in real time. It reduces alert noise, identifies genuine threats faster, and enables automated responses to mitigate risks before they escalate.
Identity and access governance ensures that only the right users have the right level of access at the right time. It minimizes insider threats, prevents unauthorized access, and strengthens overall cloud security posture.
Compliance and risk management services help organizations meet regulatory standards while identifying and mitigating potential risks. This builds trust, reduces legal exposure, and enables smoother and more secure cloud adoption.
Policy automation uses predefined rules and Compliance-as-Code to enforce governance across cloud environments. It ensures consistency, prevents misconfigurations, and enables continuous monitoring and enforcement without manual intervention.
Security posture management continuously monitors for misconfigurations and vulnerabilities, while zero trust ensures every user and device is verified. Together, they provide strong protection against breaches across complex multi-cloud environments.
We've got more answers waiting for you! If your question didn't make the list, don't hesitate to reach out.
Get In Touch With Our Experts